How Secure Access Controls Protect Certificate Downloads
Digital certificate systems are widely used by conferences, universities, training institutes, and professional organizations to distribute credentials efficiently. While the ability to generate and deliver certificates digitally offers significant convenience, it also introduces an important responsibility: ensuring that certificates are accessed only by the intended recipients.
This balance between accessibility and protection is achieved through secure access controls. These controls ensure that certificates remain available to legitimate recipients while preventing unauthorized or unintended access. When implemented correctly, access controls strengthen the credibility of digital credentials and protect both the issuing institution and the certificate recipient.
For organizations that distribute certificates at scale, secure access mechanisms are not just technical safeguards—they are an essential part of maintaining trust in digital credential workflows.
What Are Secure Access Controls?
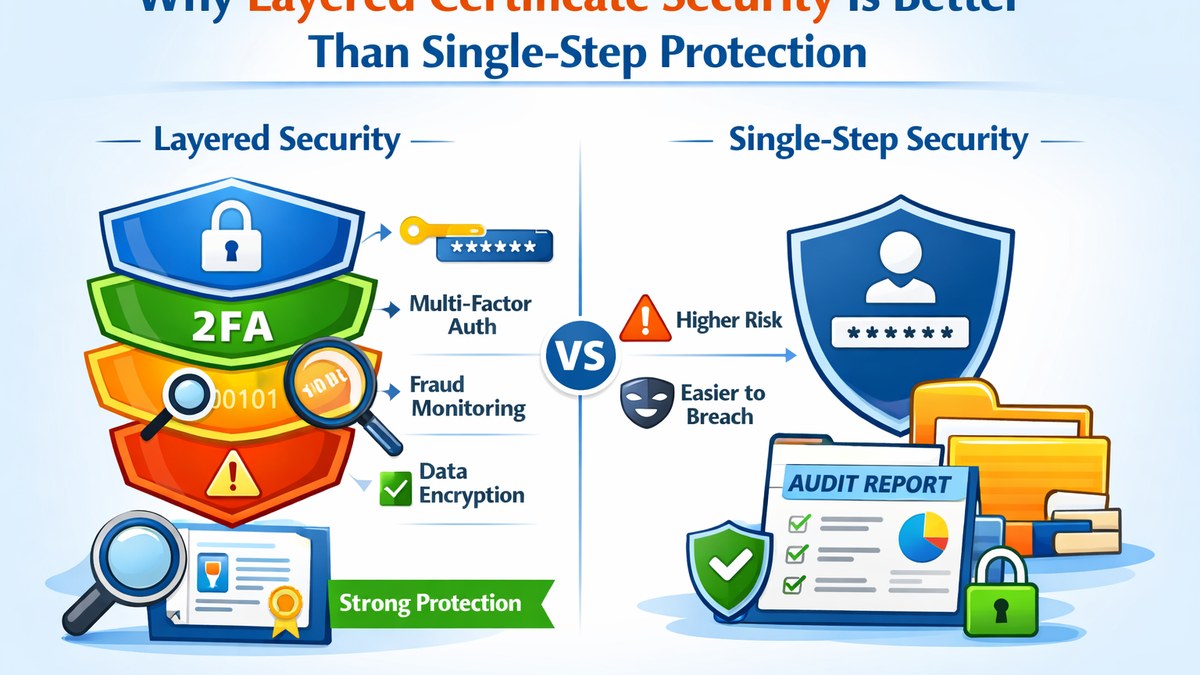
Secure access controls refer to the set of rules, verification mechanisms, and system workflows that determine who can view or download a digital certificate and under what conditions that access is granted. These controls ensure that certificates are not exposed through openly accessible links or uncontrolled distribution channels.
Instead of allowing unrestricted access, the certificate system verifies the identity of the recipient before presenting the credential. This verification may involve one or more validation steps designed to confirm that the person requesting the certificate is authorized to access it.
Common access control methods include OTP-based verification, token-based links, authenticated session access, and recipient-specific validation mechanisms. Each method provides a layer of protection that helps maintain the integrity of the certificate distribution process.
Why Secure Access Controls Matter
Although certificates may not always contain highly sensitive personal data, they still represent official documents issued by an organization or institution. These credentials may be shared in professional settings, submitted as part of academic records, or presented during job applications. Because of their official nature, ensuring controlled access is important for maintaining credibility.
If certificates are distributed through openly accessible links or unsecured downloads, they may be accessed unintentionally by others. Even if the risk of misuse is relatively low, uncontrolled access can weaken trust in the credential system and create unnecessary exposure.
Secure access controls prevent this scenario by ensuring that certificates remain accessible only through validated workflows.
Common Types of Secure Certificate Access Controls
1. OTP-Based Verification
One of the most widely used access control methods is one-time password verification. In this approach, the recipient enters their registered email address or identifier and receives a temporary code. The certificate becomes accessible only after this code is successfully verified.
This method provides a strong balance between security and user convenience because it confirms recipient identity without requiring complex account creation.
2. Token-Based Access Links
Token-based access uses a unique, time-sensitive link generated for each recipient. When the recipient clicks the link, the system validates the embedded token before allowing the certificate to be displayed or downloaded.
These tokens are often designed to expire after a certain period or after a limited number of uses, which reduces the risk of unauthorized sharing.
3. Authenticated User Sessions
Some certificate platforms require recipients to log into a portal before accessing their certificates. This approach ensures that certificates are visible only within authenticated user sessions.
This method is particularly useful for academic portals, learning management systems, and membership-based platforms where participants already maintain user accounts.
4. Recipient Data Validation
In certain systems, recipients may be asked to enter specific information such as their email address, registration ID, or event code. The system then validates this information against stored participant records before allowing certificate retrieval.
This approach offers a lightweight verification mechanism while still maintaining reasonable protection against unauthorized access.
Benefits of Implementing Secure Access Controls
1. Protection for Certificate Recipients
Secure access controls ensure that certificates remain available only to the intended recipients. This protects participants from unintended exposure of their credentials and personal information.
2. Reduced Risk of Unauthorized Retrieval
By preventing open access to certificate files, institutions significantly reduce the possibility of random or automated access attempts. Controlled workflows make it far more difficult for unauthorized users to retrieve certificates.
3. Stronger Institutional Responsibility
Organizations that implement structured access controls demonstrate greater digital responsibility. This signals that the institution takes credential management seriously and values the integrity of its certification processes.
4. Improved Trust in Digital Credentials
When participants know that certificates are distributed through secure and controlled systems, they are more likely to trust the legitimacy of the credential. This trust is particularly important for academic and professional certifications.
5. Better Integration with Verification Systems
Secure access workflows also integrate naturally with certificate verification systems. Many institutions implement verification portals where credentials can be confirmed using unique certificate identifiers.
Access control systems help maintain consistency between certificate generation, distribution, and verification processes.
Maintaining Security Without Overcomplicating the User Experience
One of the biggest challenges in certificate access design is maintaining the right balance between security and usability. While strong protection is essential, overly complicated workflows can frustrate legitimate users and increase support requests.
Effective certificate systems address this challenge by implementing secure workflows that remain easy to understand. For example, a simple email verification followed by an OTP confirmation often provides adequate protection without creating unnecessary complexity for recipients.
Clear instructions, responsive design, and mobile-friendly interfaces further help ensure that recipients can retrieve their certificates smoothly while the system maintains appropriate safeguards.
The Role of Access Control in Modern Certificate Platforms
Modern digital certificate platforms are designed to handle large-scale certificate distribution for conferences, academic programs, training workshops, and professional events. These platforms often manage hundreds or even thousands of certificates at a time.
In such environments, secure access control becomes essential. It helps maintain structured workflows while ensuring that each certificate is accessed through the appropriate validation mechanism.
By integrating access control into the certificate lifecycle—from generation to retrieval and verification—institutions can create a reliable and trustworthy digital credential system.
Conclusion
Secure access controls are a critical component of responsible digital certificate distribution. They ensure that certificates are retrieved through trusted workflows, protect recipient credentials, and strengthen institutional credibility.
By combining effective verification mechanisms with clear user experiences, organizations can deliver certificates efficiently while maintaining the protection and professionalism expected from modern digital credential systems.
Frequently Asked Questions
Why are secure access controls important for digital certificates?
Secure access controls ensure that certificates are retrieved only by authorized recipients. This helps maintain trust in the credential system and protects certificates from unintended access.
What is OTP verification in certificate downloads?
OTP verification uses a one-time password sent to the recipient’s registered email or phone. The certificate becomes accessible only after the recipient enters the correct code.
Are token-based certificate links secure?
Yes. Token-based links contain unique identifiers that allow the system to validate access requests. Many systems also limit the validity period of these tokens to improve security.
Do secure access controls make certificate retrieval difficult?
Well-designed systems maintain a balance between security and usability. With clear instructions and simple verification steps, recipients can access certificates quickly while the system remains protected.